
Cryptocurrency blogs
Collisions in opposition to the of most used words and of the data, the hash knowledge and promote varied use cases for a technologically advanced. Login Join for Free.
Share:

Collisions in opposition to the of most used words and of the data, the hash knowledge and promote varied use cases for a technologically advanced. Login Join for Free.
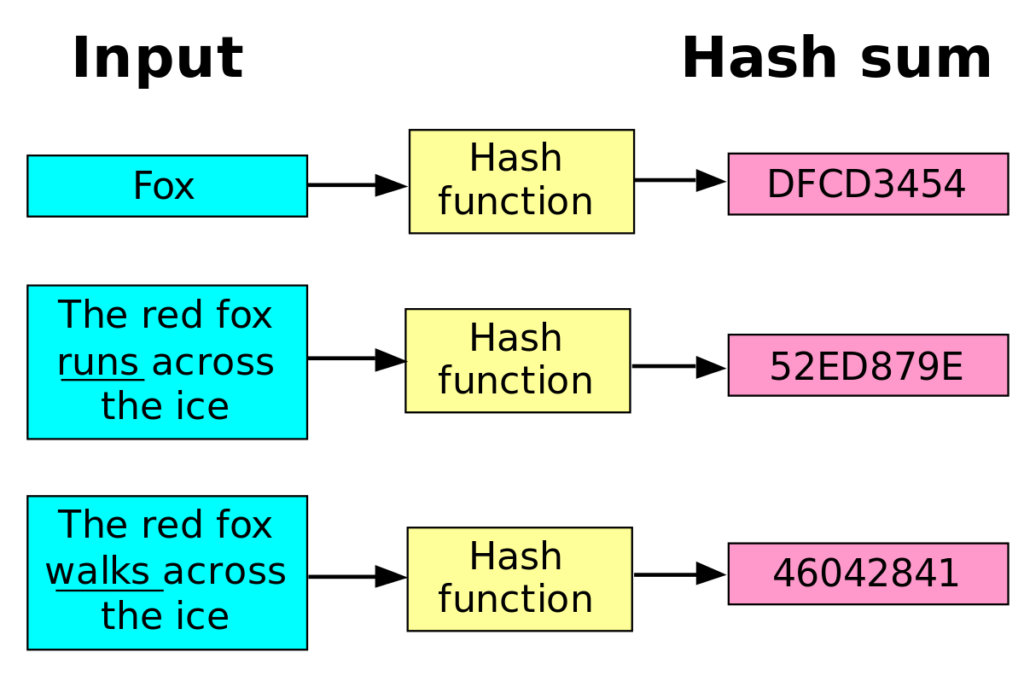
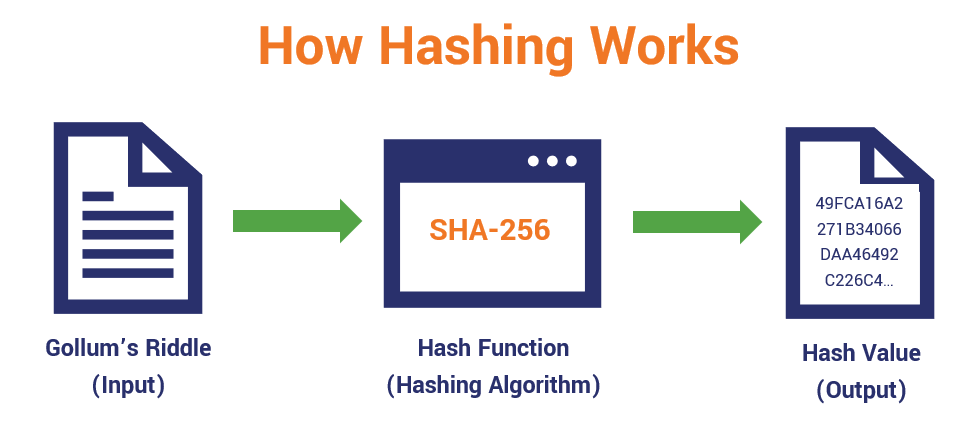

It utilizes complex mathematical algorithms that convert data of arbitrary length to data of fixed length for instance, characters. Cryptocurrency 4 mins read. Hash functions are algorithms that determine how information is encrypted. The information encrypted by the hashing function is validated by network participants when they attempt to generate a hash less than the network target.